I’d always found foursquare a bit peculiar. What could possibly compel a person to get up early after a Friday night of partying and hurry to the other side of campus to click a button on their phone and ‘check in’? Why were foursquare locations popping up for the most arbitrary of things…Classroom 6 in Old Chem, a local frat house, or even my dorm’s 3rd floor bathroom. I noticed that foursquare was gaining popularity and I really couldn’t figure out why. Yes, the service lets you tell everyone where you are every second of every day, and yes, it lets you brag to your other foursquare pals when you become the ‘mayor’ of a location both of you were fighting over – whether it be the Duke Chapel or the dorm bathroom. To me, foursquare was a stupid game - one that I thought could easily be cheated.
I originally had no intention of hacking foursquare - I just wondered whether I could do it. I knew that HTTP had no inherit location header that foursquare could take advantage of, so they would have to get the user’s location one layer up – the API level. And I knew foursquare had a public api. This lead me to the hypothesis that I could probably pass false GPS coordinates to the foursquare API, and check in to any location near that location. I did a quick google search to confirm. It turned out to be even easier than that. According to KrazyDad in his blog post Mayor of the North Pole, you didn’t even need to pass coordinates to foursquare’s api – you simply pass a venue id (a location’s id) to the check-in api url, and foursquare will credit you as having checked in and been there.
I now knew, in theory that it could be done. But I wanted to actually get a script working that could do it. Not just a script that could commit check-in fraud, but one that could commit mayorship fraud. A hop, skip, and a jump later, this PHP script was born. Feel free to test the script yourself…all it requires is a PHP server (with curl installed) and a browser window. The venue id of a location can be found by going to the locations page on foursquare. For example, the White House’s venue id is 3945, which I found via its foursquare url: https://foursquare.com/venue/3945. I will probably be publishing an entirely javascript version soon so anyone with a web browser can run the script.
In under 40 lines of code, I had created a script that would, every day, automatically check me in to a number of locations, eventually taking the mayorship of those locations. Further testing of the script showed that you can check in to any location as long as it is somewhat near the last location you checked in to. Checking into a bar in Durham, NC and then an hour later to the White House in Washington, DC. worked. Rome and then Washington, DC in an hour didn’t. Presumably, if you wanted to check in to many places throughout the country, you just create a ‘check in path’ from the first check in location you want to the last, in geospatial order.
Yes there were fraud detectors, but I got around them. Like I said above, check ins too far away from one another over too short of a time period would be seen as invalid. Checking in to a location more than once a day was seen as invalid. But with patience, over the course of one or two months (depending on the locations popularity) this script would make me the mayor of that location, with no effort on my part, no matter where in the world I am, and keep that mayorship for however long I wanted it.
Wanting to expose Foursquare’s flaws to its many worshipers on campus, I put the venue ids of Duke’s top locations into my script – the Duke Chapel, the Duke Gardens, Cameron Indoor Stadium, and even Shooters. Within a month I owned them all. People came up to me, and said, how did you do that? Ironically, stealing away foursquare mayorships was a great way to meet girls – they were the vast majority of foursquare users at Duke. Not wanting to offend any lovely ladies, I didn’t tell them I was hacking. The free wings Hooters offered to foursquare users every fourth check-in also encouraged me to keep my mouth shut.
One day, Duke’s own CS professor, Owen Astrachan, stopped me in the halls and asked me how I’d managed to steal the mayorship of his favorite on campus eatery while he and another CS professor had been constantly battling back and forth for the mayorship for over 2 months. Surprised the CS professors had not seen the fault in the service they used so frequently, I spilled the beans to him. He laughed, asked me some questions, and walked away. Months later, I heard Duke foursquare hacker ‘Joe L’ was part of the course topic ‘Ethical Hacking’ in Astrachan’s 400 person intro CS course: ‘Technical and Social Analysis of Information Science’. Then another 2 weeks went by. I heard from a friend on the ‘foursquare committee’ (a group that promotes foursquare’s use on campus at Duke) that the group was trying to figure out how to stop the infamous Joe L from basically halting foursquare’s use at Duke. The end of the month came around, and I went to a Chronicle event. At the event, I was approached by my boss’s boss’s boss, a very angry, 90-pound girl, who had just learned I had stolen all of her Chronicle mayorships by cheating. This girl had plenty of reason to be upset – she came to the office every day to make sure the Chronicle paper came out on time in top quality. She wanted recognition for that, which she sought by being the mayor of the Chronicle offices on foursquare. My script had stolen that from her. Like this girl, many people became aware of how I was doing what I was doing, and got a little angry. Wanting to retain my job at the Chronicle, wanting to cool people down, and feeling I had made my point, I deleted all the Duke locations from my script. Slowly, my name faded from the mayorship position on over 30 Duke locations.
But there was one location for which I kept the script running – the White House. I wanted to prove this script could truly disrupt foursquare, so I went after one of the most checked-in to places in the country – the president’s pad. And after about 2 months, I was unrightfully crowned mayor of the White House…a position almost as prestigious as President. Two days after becoming mayor, I was banned from foursquare, after almost 5 months of abusing the system:
Hi there,
Our system has flagged your account due to frequent check-ins when you’re not actually at a place. While we love that you’re an enthusiastic user, it’s important to follow our guidelines in order to ensure the best experience for everyone! Please only check in when you’re spending time somewhere and your check-ins will be legitimate.
Thanks! Parker
I don’t think its a coincidence that I was banned right after becoming the mayor of such a high profile location. My best guess is the former mayor of the white house reported me, as I had gone so long without getting caught I doubt I was automatically ‘flagged’ by the system. This leads me to believe that the fraud detection system at foursquare is not very good – even if they did automatically catch me after 5 months of abusing the system, 5 months is a long time. Even after the ban, there was nothing stopping me from creating a new account, putting its credentials into my script, and doing it all again.
I would love to provide foursquare screenshots of all this, but when I was banned my account was deleted so I can’t take any screenshots of it. But I do have some twitter posts from that time.
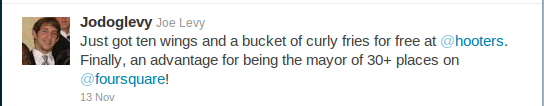
A few weeks ago in the middle of the night I received a call from Pennsylvania. ‘Are you the dude who hacked foursquare and ran ****?’ the drunk person on the other end of the phone said. He proceeded to call me the next Mark Zuckerberg because of my ability to do this. While I liked the compliment, I was getting way more credit than I deserve. Foursquare makes it very easy to abuse their service, and actually have no technological way to prevent location fraud if they want to use a public API. People don’t know just how easy it is to abuse the service. So I wrote this post. People need to know its not worth it to wake up early and run across campus to retain your mayorship, when a kid anywhere in the world can use a script like mine to beat you while he sleeps. Merchants need to know that they shouldn’t offer discounts or incentives to people who check-in, or their mayors, because a script like mine can get any number of abusers free stuff whenever they want, at any of the places that give foursquare discounts.
Many people will probably dislike that I am providing a means for others to cheat. That is true, I am. But really what I am doing is providing full disclosure to a system that does not work. A system consumers, merchants, and VCs should not get over invested in because of how easy it is to manipulate. Feel free to keep using foursquare…but do so knowing it is a game with many loopholes.
Update: Since foursquare implemented OAuth, the script linked to in this post no longer works. I was able to get around this and automate checkins with a new script, but that’s a story for another day…